These Dangerous Viruses Can Steal Your Cryptocurrency
If you’re a crypto holder than as cryptocurrency market value grow you should concern more about your crypto fund’s security.
If you still not aware about the security of your funds then you have a bigger chance of being a victim of hacking attacks.
Yes… that’s why you should know some of the popular attacks used by hackers to steal your cryptocurrencies.
Ok, now look at some dangerous viruses created by hackers to steal cryptocurrencies from holders.
WannaMine.
It is a powerful and most famous cryptojacking virus, it became popular after the WannaCry attack in 2017.
Basically, this virus designed to mine Monero coin.
Firstly the attacker somehow manages to insert WannaMine script on victim computer after that malware silently infects a victim’s computer, and then uses it to run complex decryption routines that create new Monero.
The currency is then added to a digital wallet belonging to the hackers, ready to be spent whenever they choose.
Above is a common working pattern of almost all cryptojacking viruses but WannaMine is very dangerous just look at below some stats then you will realize.
- This virus affected more than the 500,000 systems between September 2017 and February 2018!.
- WannaMine consumes almost 100% of CPU power to mine coin that directly causes a bad effect on system performance and power consumption.
Just imagine being a WannaMine victim.
Being this virus victim means throwing away the system and paying a huge electricity bill.
But don’t worry there is a patch available and you just need to constantly upgrad your system and use a trustworthy latest antivirus software to get away from WannaMine.
And don’t forget to check your system performance regularly.
Razy Trojan.
This Trojan became popular in early 2019.
This virus is come with software and browser extensions.
The Software is typically distributed via websites, advertising banners and free file hosting services that disguise themselves as legitimate software.
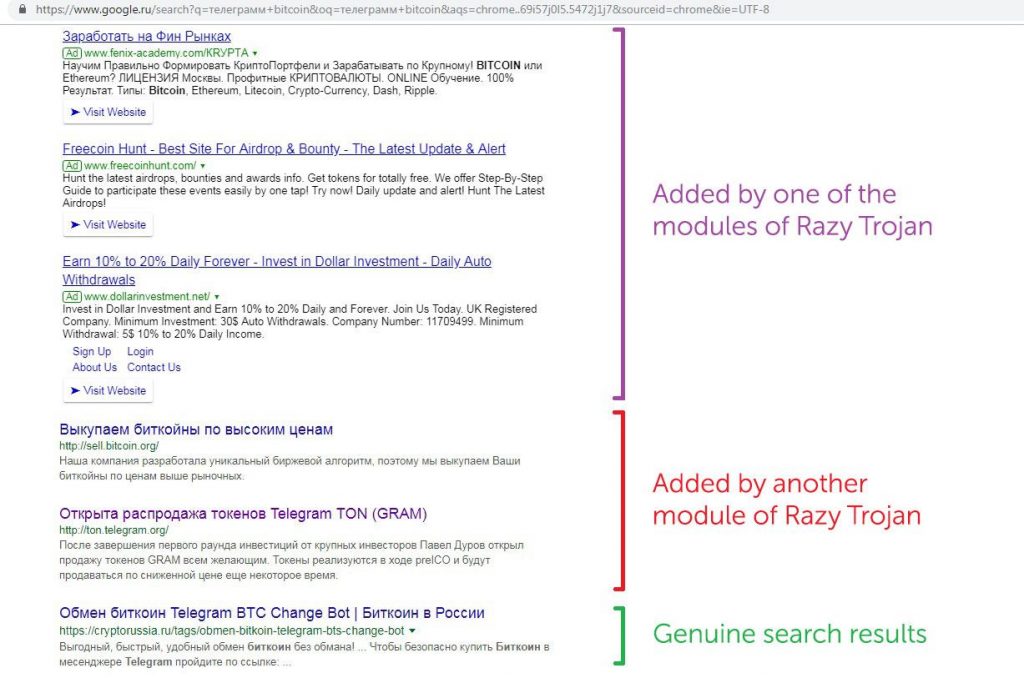
And malware can be installed onto Google Chrome extensions, as well as Mozilla, Firefox and Yandex Browsers.
That malware can disable automatic updates and bypassing the “integrity checks” that are often required for such files to move forward.
After installation
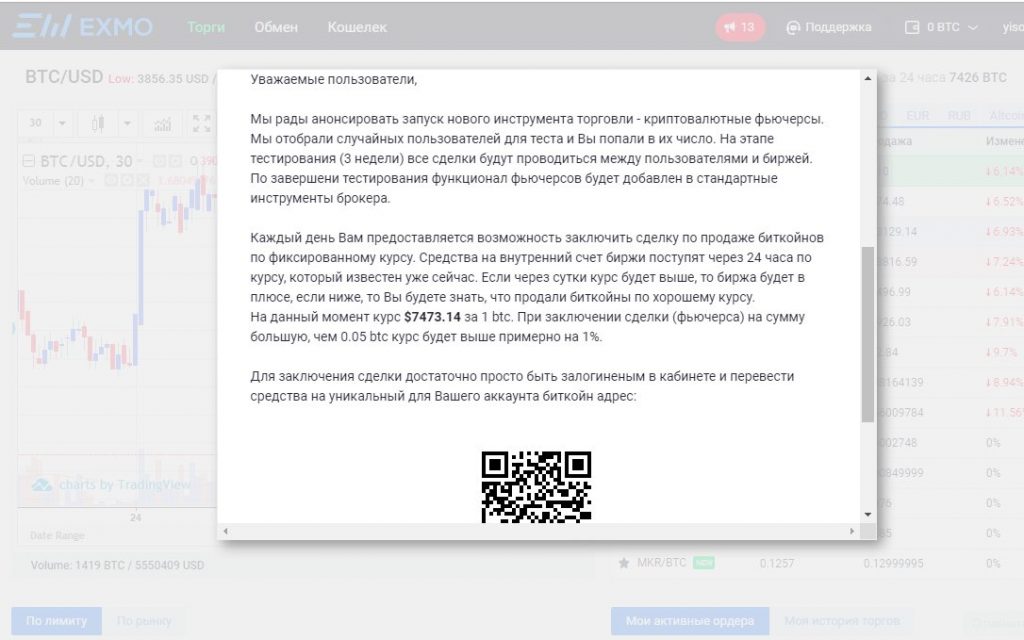
Also, It can mix up Google and related search engines search results to potentially trick people into examining infected sites.
If you visit the infected site or click any fake popup message then there is no guarantee of your crypto safety.
Because this virus uses social engineering methods like giving the offer to earn free Bitcoins or asking crypto donations for some disasters.
If you give your crypto believing that I am going to be rich in 2 days! or donate crypto with sympathy, believe me, that crypto will fill up cybercriminal’s wallet.
But don’t worry because security patch is available for this virus and please be careful and don’t install any untrusted software and do not click any suspicious links.
Coinhive.
It is a malicious javascript code that runs in website and free browser extensions.
This virus is also a famous cryptojacking virus that mines Monero(XMR).
The malicious code runs only if you visit a website that uses this code or using any browser extension that has Coinhive code in it.

One drawback of this virus is this virus won’t work if you completely close your browser sometimes is better to reset your browser completely.
That’s why check your task manager when your computer fan making noise without resting.
And, if the task manager shows browser utilizing more than 90% of CPU power without any specific reason for a long time, then it is better to completely reset your browser.
Also, you can check your browser task manager ( I believe that Chrome is the only browser that provides task manager option within the browser).
Once this virus started to run then it will hurt your CPU performance badly that’s why better to reset your browser is the best option in my opinion.
One crazy fact is Coinhive have their own website that provides malicious javascript to website admin (I am not using it) for mine Monero coin.
CryptoLoot is another service that offers the same features as Coinhive and they have their own website too.
Conclusion.
Crypto viruses is not a new thing now because as the crypto market grows new virus born to steal crypto by using new methods.
The difference is that now they not only limited to Desktop or PC’s, now new virus can affect mobile users too.
The best example is earlier 2019 fake Metamask app fund in Google Play Store that app capable of replacing copied cryptocurrency wallet addresses with an address belonging to an attacker.
The fake app uses malware called ‘Clipper’ to replace wallet address.
Now the
Because smartphones are common devices used by crypto holders and they are vulnerable for many attacks.
These incidents show hackers now find new ways to steal money from innocent crypto users.
But as a crypto community, we can avoid these attacks by spreading news and educating our selves and others.
If you find this article is helpful, then please share it your friends and family members.
If you have any points to add or any suggestions to give, then please mention those in comments.
